Introduction
Electronically controlled RF systems include radar, electronic warfare (EW), and communications. The RF environments that these types of systems operate in are complex and sometimes hostile. For example, a repeater jammer can repeat the received radar signal and retransmit it to confuse the radar, which is also called spoofing.
Here we present the creation of a custom implementation of a jammer for use within the Extended Mobile Ad-hoc Network Emulator (EMANE) real-time network emulation framework. EMANE is a real-time network emulation environment for analysis and testing of mobile ad hoc wireless networks (MANETs).
Electronic Jamming Definition
Radio jamming is the deliberate jamming, blocking or interference with authorized wireless communications. In some cases jammers work by the transmission of radio signals that disrupt communications by decreasing the signal-to-noise ratio. The concept can be used in wireless data networks to disrupt information flow.
Jamming is usually distinguished from interference that can occur due to device malfunctions or other accidental circumstances. Devices that simply cause interference are regulated under different regulations. Unintentional ‘jamming’ occurs when an operator transmits on a busy frequency without first checking whether it is in use, or without being able to hear stations using the frequency. Another form of unintentional jamming occurs when equipment accidentally radiates a signal, such as a cable television facility that accidentally emits on an aircraft emergency frequency.
Electronic Jamming Types
The purpose of jamming is to block reception of transmitted signals and to cause a nuisance to the receiving operator. Intentional communications jamming is usually aimed at radio signals to disrupt control of a battle. A transmitter, tuned to the same frequency as the opponents’ receiving equipment and with the same type of modulation, can, with enough power, override any signal at the receiver. Digital wireless jamming for signals such as Bluetooth and WiFi is possible with very low power.
The most common types of signal jamming are:
- random noise,
- random pulse,
- stepped tones,
- warbler,
- random keyed modulated continuous waveform (CW),
- tone,
- rotary,
- pulse,
- spark,
- recorded sounds,
- replay attacks,
- gulls, and
- sweep-through.
Digital signals use complex modulation techniques such as QPSK. These signals are very robust in the presence of interfering signals. However, the signal relies on hand shaking between the transmitter and receiver to identify and determine security settings and methods of high level transmission. If the jamming device sends initiation data packets, the receiver will begin its state machine to establish two way data transmission. The influence of the jammer causes the receiver to loop back to the beginning instead of completing the handshake. This method jams the receiver in an infinite loop where it keeps trying to initiate a connection, but never completes it, which effectively blocks all legitimate communication.
Blue-tooth and other consumer radio protocols such as WiFi have built in detectors so that they transmit only when the channel is free, that is carrier sensing. Simple continuous transmission on a given channel will continuously stop a transmitter for transmitting, hence jamming the receiver from ever hearing from its intended transmitter.
These are examples of wireless denial-of-service (WDoS) types of attack. Recent studies, demonstrate that such attacks can be very easily accomplished using off-the-shelf equipment.
Other jammers work by analyzing the packet headers, and depending on the source or destination, selectively transmit over the end of the message, corrupting the packet.
Anti-Jamming Techniques
Channel hopping, or switching from one channel to another, is the most popular countermeasure to jamming. Proactive channel hopping is the simplest implementation. Frequency agility can be an effective technique to counter the signals generated from interference sources and help support effective operations of these systems.
For example, consider a scenario with a stationary monostatic radar and a moving aircraft target. A jammer generates a spoofing signal which confuses the radar. Once the radar detects the jamming source, frequency agility techniques can be employed which allows the radar to overcome the jammer’s interference to allow communicating with the moving target aircraft.
EMANE Custom Jammer
To support the design and development of frequency agile based systems, whose waveforms are being evaluated a part of the EMANE network emulation environment, it is essential to provide jamming signal sources to evaluate the effectiveness of the anti-jamming technologies. We developed a custom jammer to add jamming content to an EMANE network emulation to facilitate evaluating system performance in the presence of jamming.
The EMANE Network Emulation Module (NEM) protocol stack supports customization through the development of custom “shim” layers that exist as part of the executing NEM software stack. A custom shim layer is inserted between component layers in an NEM layer stack without requiring those components to have knowledge of its presence. The EMANE shim architecture is described in greater detail in the post EMANE Networking Waveform Emulation.
A primary benefit of frequency agile communications with Anti-Jam (AJ) mode or cognitive AJ radio systems (CARS) is the system detects through spectrum sensing the characteristics of an interferer, and responds to attempted jamming of the communications. To introduce jamming into the network emulation environment for evaluating system responses, a custom jammer “shim” layer was developed which executes within a separate Linux container (LXC), and is started and stopped dynamically using the EMANE event subsystem, which consists of messaging to all NEMs.
Since the jammer shim executes within an LXC, as does all EMANE Network Emulation Nodes (NEMs) where LXC is used for virtualization, the jammer node is a full citizen of the EMANE network. The jammer NEM has IP addresses assigned to its exposed interfaces and a unique NEM id, as does all NEMs. An SSH connection can be made to the jammer’s Linux container for monitoring and control of the processing running within the jammer LXC, which will at a minimum be EMANE and the NEM stack, sshd, and can also include other executable applications.
The jammer NEM can have other real-time applications executing within the jammer LXC, such as network management applications (e.g. OLSR or OSPF). The jammer shim architecture is based on the full EMANE NEM stack, and as such, opens the jammer to sourcing and sinking and processing network traffic. The jammer based shim has a unique NEM identifier, as does all EMANE NEMs, and therefore can be the specific target of EMANE messaging and events to dynamically set attributes such as path-loss and GPS location .
For our unique network emulation testing purposes, we needed the EMANE jammer to produce a 1024 point Power Spectral Density (PSD) waveform signature onto the EMANE over-the-air (OTA) control bus. The content of the PSD is dynamically created based on the jammer configuration, which includes center frequency, bandwidth, signal levels, noise levels, etc. The created PSD waveform is displayed in our custom EMANE OTA viewer as described in the post EMANE Real-Time Spectrum and Waterfall Viewer.
EMANE Jammer Operating Modes
The jammer “shim” is configured for various operating modes to match common jammer types as follows:
- Fixed frequency (CW tone) at a configured center frequency and bandwidth.
- Sweep frequency (sweep through tones) between a start and stop frequency with sweep frequency step interval and sweep rate.
- Hop-set frequencies (stepped tones) with sweep rate and optional random ordering.
The following figure provides a spectral and waterfall plot for 4 concurrently operating jammers, one operating in CW tone mode using a fixed frequency of 1.3 GHz with random noise applied to the signal, two are sweep frequency mode jammers operating with different signal levels and sweep rates, and one is a hop-set mode jammer operating at a different sweep rate. This spectrum/waterfall content is rendered using our custom real-time EMANE OTA viewer.
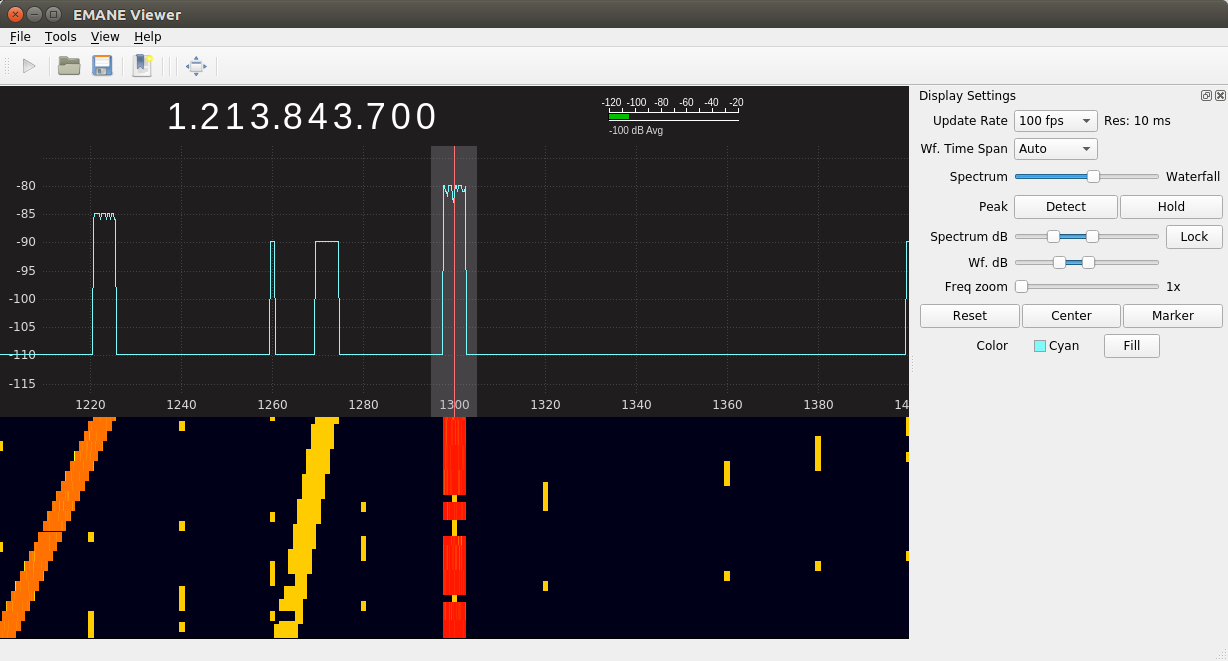
Figure 1: Spectrum/Waterfall View of Concurrent EMANE Jammers
EMANE Jammer NEM Configuration
The custom jammer shim sits below the EMANE PHY layer in the EMANE NEM configuration XML file. This is illustrated by the following XML configuration file nem.xml whose contents represents the NEM configuration for a jammer node. Multiple jammer nodes are included in a typical EMANE emulation configuration, each operating within a separate LXC, and operating with different operating characteristics through different configurations.
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE nem SYSTEM "file:///usr/share/emane/dtd/nem.dtd">
<nem type="unstructured">
<phy>
<param name="noisemode" value="all"/>
<param name="noisemaxsegmentduration" value="2000000"/>
</phy>
<shim definition="jammerphyshim.xml"/>
</nem>Figure 2: Custom EMANE Jammer Shim NEM Configuration File
EMANE Jammer Shim Configuration
The following XML configuration file is used by the jammer shim to control its operating behavior. Many of the settings listed are used for populating the fields of the EMANE Common PHY Header.
- The subid field is used within the EMANE system to determine whether or not the signal is considered in-band our out-of-band with the other waveforms being emulated.
- The bandwidth in KHz of the transmitted jammer signal is specified by the bandwidthkhz field.
- The psdtxpower and noisefloor setting define the signal levels for the generated PSD metadata.
- For fixed frequency CW operating mode, the center frequency is configured to a fixed value from the centerfreqkhz setting.
- When operating in sweep frequency mode, the jammer will sweep between the settings specified by startfreqhz and stopfreqkhz using the frequency steps specified by stepfreqkhz.
- 10 hop frequencies are specified for hop-set frequency mode of operation.
- For both sweep frequency and hop frequency operating modes, the ratefps configuration specifies the sweep rate of the jammer signal in frames per second (FPS).
- Noise can be added to the transmitted jammer signal based on the noiseenable, noisefloor, and noisemax settings.
- The randomfreqenable setting, when enabled and operating in frequency hop-set mode, will cause the jammer to randomly transmit on a center frequency specified in the hop-set rather than in the order of the hop-set frequencies specified in the configuration file.
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE shim SYSTEM "file:///usr/local/share/emane/dtd/shim.dtd">
<shim name="Jammer PHY Shim" library="jammershim">
<param name="autostartenable" value="true" />
<param name="bandwidthkhz" value="1000" />
<param name="centerfreqkhz" value="1300000" />
<param name="freqsegmentpower" value="44.149733" />
<param name="hopfreq1khz" value="1200000" />
<param name="hopfreq2khz" value="1220000" />
<param name="hopfreq3khz" value="1240000" />
<param name="hopfreq4khz" value="1260000" />
<param name="hopfreq5khz" value="1280000" />
<param name="hopfreq6khz" value="1300000" />
<param name="hopfreq7khz" value="1320000" />
<param name="hopfreq8khz" value="1340000" />
<param name="hopfreq9khz" value="1360000" />
<param name="hopfreq10khz" value="1380000" />
<param name="mode" value="0" />
<param name="noiseenable" value="false" />
<param name="noisefloor" value="-110" />
<param name="noisemax" value="20" />
<param name="passupstreampackets" value="false" />
<param name="psdtxpower" value="0" />
<param name="randomfreqenable" value="false" />
<param name="ratefps" value="1" />
<param name="registrationid" value="8" />
<param name="startfreqkhz" value="1200000" />
<param name="stepfreqkhz" value="1000" />
<param name="stopfreqkhz" value="1400000" />
<param name="subid" value="4" />
<param name="txantennagain" value="0.0" />
<param name="txbandwidthkhz" value="5000" />
<param name="txpower" value="0.0" />
</shim>Figure 3: Custom EMANE Jammer Shim Configuration File
EMANE Jammer Shim Operation
The jammer shim utilizes the messaging associated with the EMANE event subsystem, which are broadcast to all NEMs. EMANE events are issued on the host computer in a terminal session rather than within the guest Linux container using a secure shell connection to the container. The jammer can be dynamically turned on by sending an event to the NEM id of a particular jammer, which begins jammer signal transmission onto the EMANE OTA control bus, or off, which terminates this activity. The autostartenable setting can be used to automatically start the jammer activity upon network emulation initialization.
Conclusion
EMANE is an industry leading network emulation framework for real-time design and analysis of networking systems. The addition of jamming capability is essential to analyzing and testing frequency agile systems and anti-jamming technologies. The custom jammer development for the EMANE network emulation environment introduces highly customizable multi-mode jamming capabilities into the EMANE framework as a fully functional EMANE NEM.
EMANE events are issued on the host computer in a terminal session rather than within the guest Linux container (which uses a secure shell connection to the NEM container).
In the EMANE propagation model, transmit path-loss within the physical layer model is based on either location or path-loss events.
As a fully functional NEM, the jammer can be the target of the EMANE event subsystem, such as dynamically setting the transmit path-loss real-time based on external propagation calculations, or having path-loss dynamically calculated based on jammer and radio GPS location events. This allows the transmit signal level of the jammer to vary between receiving nodes. The EMANE event subsystem is also used to dynamically start and terminate the generation of jamming content on to the EMANE OTA control bus.

